当你的服务器受到 CC 攻击时,系统负载就会爆增,这时候就可以利用此脚本自动检测系统负载,当压力超过一定的值时就可以切换为” I’m Under Attack! “模式了。
官网 :https://github.com/Machou/Cloudflare-Block
首先到官网下载脚本或者本站下载:
wget https://www.7198.net/Shell/cloudflare-block.sh && chmod +x cloudflare-block.sh
cloudflare-block.sh 脚本:
#!/bin/bash
# $1 = 1min, $2 = 5min, $3 = 15min
loadavg=$(awk '{printf "%f", $1}' < /proc/loadavg)
# load is 10, you can modify this if you want load more than 10
maxload=10
# Configuration API Cloudflare
# Your Global API Key (https://dash.cloudflare.com/profile)
api_key=
# Email of your Cloudflare account
email=
# Zone ID (https://dash.cloudflare.com/_zone-id_/domain.com)
zone_id=
# Default security level when there is no attack, see in readme
default_security_level=high
# Whether to write debug messages to the debug.log file under script dir
debug=0
basedir=$(dirname "$0")
attacked_file=$basedir/attacked
[ "$debug" -eq 1 ] && exec > "${logfile:-$basedir/debug.log}"
# You can put aforementioned config values either in-place
# or in the file named 'config' in the script's directory.
config_file=$basedir/config
[ -e "$config_file" ] && source "$config_file"
api_set_mode() {
local mode
mode=$1
curl -s -X PATCH "https://api.cloudflare.com/client/v4/zones/$zone_id/settings/security_level" \
-H "X-Auth-Email: $email" \
-H "X-Auth-Key: $api_key" \
-H "Content-Type: application/json" \
--data "{\"value\":\"$mode\"}" \
|| echo "Error: failed to set security level to $mode"
}
# create file "attacked" if doesn't exist
if [ ! -e "$attacked_file" ]; then
echo 0 > "$attacked_file"
fi
was_under_attack=$(cat "$attacked_file")
under_attack=$(echo "$loadavg > $maxload" | bc)
if [[ "$1" != [01] ]]; then
echo "Incorrect usage! Please pass either 0 or 1 as an argument"
exit 1
fi
if [ $debug -eq 1 ]; then
echo "Mode: $1; was under attack: $was_under_attack; now under attack: $under_attack"
echo "Load average: $loadavg"
fi
if [ "$1" -eq 0 ] && [ "$was_under_attack" -eq 0 ] && [ "$under_attack" -eq 1 ]; then
# attack just started and we want to enable under-attack mode
# Activate protection
[ "$debug" -eq 1 ] && echo "Activating under-attack mode!"
echo 1 > "$attacked_file"
api_set_mode under_attack
elif [ "$1" -eq 1 ] && [ "$was_under_attack" -eq 1 ] && [ "$under_attack" -eq 0 ]; then
# attack just finished (and up to 20 minutes passed since)
# and we want to disable under-attack mode
# Disable Protection
[ "$debug" -eq 1 ] && echo "Leaving under-attack mode!"
echo 0 > "$attacked_file"
api_set_mode "$default_security_level"
fi
exit 0
修改 cloudflare-block.sh 配置:
#您的 cloudflare API 密钥(https://dash.cloudflare.com/profile) API_KEY= #您的 Cloudflare 帐户的电子邮件 email= #Zone ID(https://dash.cloudflare.com/_zone-id_/domain.com) zone_id= #没有攻击时的默认安全级别,请参阅 Cloudflare 帮助文件 default_security_level=high #是否将调试消息写入脚本目录下的 debug.log 文件 debug=0
脚本默认的是检测系统负载为 10,启动” I’m Under Attack! “模式,可以根据需要来调整,一般可以简单的设置为你的核心数*1.2 比如你 CPU 是双核的,可以设置为 2.4
maxload=7
设置定时任务,如果未启用保护,每 1 分钟检查一次,负载高于 7 开启 5 秒盾。如果启用保护,则每 20 分钟检查一次,负载降为 7 以下时取消 5 秒盾:
*/1 * * * * /root/cloudflare-block.sh 0 */20 * * * * /root/cloudflare-block.sh 1
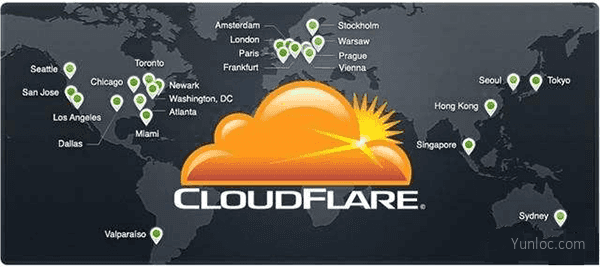
Cloudflare 是一个非常好用的防御 DDos 和 CC 攻击的工具,免费版本的 Cloudflare 结合 API 可以实现更加灵活的功能,对于普通的防御足够自己使用了。
 798VPS
798VPS
最新评论
十塊年費是直接從這張卡裡的外幣按匯率扣?
有人申请成功了吗?我的已经两天了,没有消息,没有收到成功邮件。信用卡扣了款!